In Part 1 we created VNet and in Part 2 we talked about how to create new VM. Once your VM is deployed, it’s ready to be used for whatever purpose you have for it. But you’ll probably want some of VMs to be accessible from outside your VNet, especially if this VM is webserver with IIS role installed.
For this we need to configure NSG – Network Security Group. NSG contains a list of Access Control List (ACL) rules that allow or deny specific traffic on your VM in your VNet. NSG can be associated with either subnet in VNet or individual VM instance where subnet rule applies to entire subnet and individual rule applies to specific VM.
In this case we’ll talk about opening port 80 (http) so your webserver can be accessed over internet. I also got lot of questions about this specific subject (in person, e-mail, forums) as a lot of people have issue setting up HTTP in ARM.
First go to ‘Virtual Machines’ in Azure portal.
Select VM with IIS role from list of your VMs.
In new tile, select ‘Network Interfaces’.
Click on your network interface.
In new tile select ‘Network Security Group’.
Select security group to edit.
In new tile, select ‘Inbound security rules’.
Click ‘Add’ and wait for new tile to open.
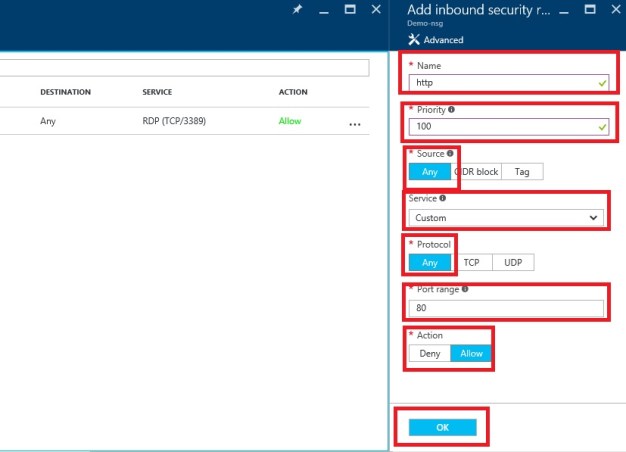
You need to enter parameters for new rule. First enter name for your rule (‘http’ in this case but can be anything, I just find it easier to manage when name tells me what it’s about), set priority to ‘100’, Source to ‘Any’, leave service as ‘Custom’, set protocol to ‘Any’, enter 80 for port range and set action to allow. Finally click OK and wait for few seconds (this can vary but usually it’s created under 1 minute).
Once your rule is created, go to your VM overview page and check your Public IP address/ DNS name.
Enter your IP address to browser and here it is – your IIS server is accessible from internet and ready to be used.










Comments are closed.